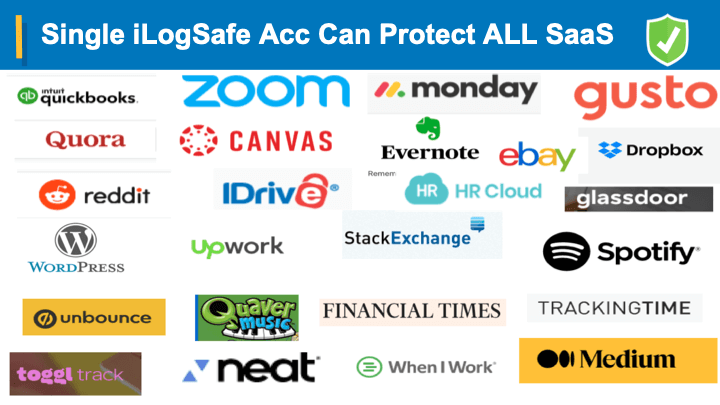
Safely manage multiple accounts with a single disposable dynamic credential
Zero-footprint MFA Enterprise Grade Security
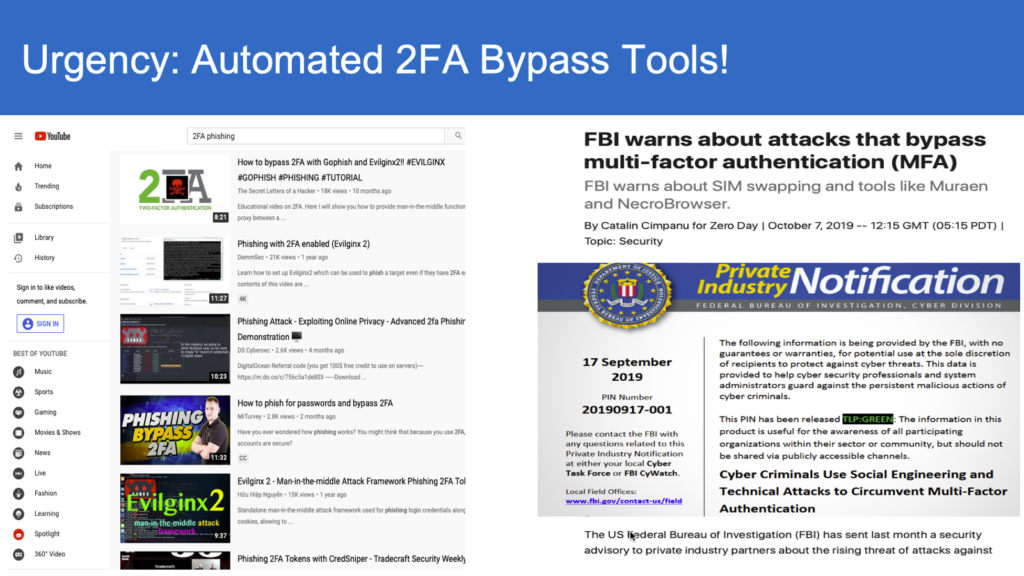
- Eliminate risks associated with password vulnerabilities
- 100x protection against key logging malware
- 1000x protection against Phishing (No passwords)
- 5x resilient even when server compromised
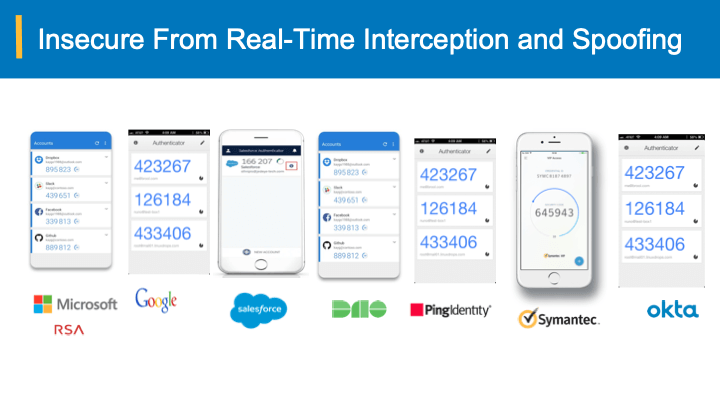
- Built in Man- Built in Man-in-Middle protection
Our technology offers the most secure alternative to password management
Turnkey User Authentication Systems
iLogSafe Authentication System (UPCAS) strikes a perfect balance between convenience and safety. With the current technologies, end-users are often overwhelmed with the sheer number of options and practices and in the end only to find out that many layers have been added without necessarily providing the desired (or enhanced) security. The next generation UPCAS is based on Java and other standard technologies, and thus can be easily integrated with any standard’s compliant systems. UPC technology is backward compatible with all the authentication mechanisms, and thus the transition towards this leap-frog technology is achieved smoothly without necessarily disrupting and uprooting the existing systems.
- Cost effective: a payback period of less than a year
- Easy to use: end users do not need additional devices or software
- Scalable: easily deployed in mass-roll out situations
- Versatile: usable across multiple industries
- Robust: backward compatible with all the authentication mechanisms
Benefits of Passwordless Authentication
- Elimination of password management costs
- Better compliance with 2X savings on PCI Better compliance with 2X savings on PCI DSS,HIPAA,FFIEC DSS,HIPAA,FFIEC
- Enterprise grade Single Sign On (SSO) enabling password- ALL PASSCODES –NO PASSWORDS
- Enterprise grade Single Sign On (SSO) enabling password- less application access less application access
- Fraud prevention and transactional authentication
UPCAS features include:
- Platform agnostic
- Minimal requirements (commercial of the shelf) on the supporting hardware/software
- Highly scalable architectures
- N+1 and geo-redundancy
- Easily integrable with all dashboard systems
- Plug-n-play systems
- Customizable and offer Internationalization of features
- Single sign on (SSO) and other extensions
- Monitoring and alerts
security solutions
Strong authentication for all industries
Robust, easy-to-use digital security solutions for multi-industry